The Oldest Trick in the Book - North Korea's Cyber Programme and the Shadow Economy of Embargoed States
Overview
Trafalgar, 1805. The British Royal Navy, under Admiral Horatio Nelson, destroyed the combined Franco-Spanish fleet in the waters off southern Spain. Nelson died on the deck of HMS Victory, and Britain’s naval supremacy was confirmed beyond question. Napoleon Bonaparte, master of half a continent, accepted a reality he could not fight his way out of; he would never control the seas while Britain’s Navy existed. So, he changed tack.
If Britain could not be beaten militarily, it would be strangled economically. The Berlin Decree of 1806 declared a continental blockade, every European port under French influence or control was forbidden from trading with British ships or accepting British goods. The idea was that strangling Britain during wartime and cutting off their export trade would cause Britain’s economy to collapse, where they would then sue for peace.
Problem is, customs officials right across Europe were on the british payroll, goods were repackaged and relabelled, and Britain’s smuggling operation was a huge success and kept the British economy running; by running small boats past French lines under the cover of darkness.
Throughout history, one of the most powerful weapons one nation can wield against another requires no army, no navy, and no declaration of war. It requires only leverage, control over trade routes, financial systems, and the flow of goods. Economic strangulation has been a tool of statecraft for as long as states have existed. Cut off a nation’s access to markets, deny it the materials it needs to function, then it will bend, collapse, and eventually capitulate.
I am a keen student of history and philosophy when I’m not doing cyber, and its easy to see parallels across history and what we’re seeing in the modern day. I thought I’d write this blog to make a case study of North Korea, and how state-enabled cybercrime plays a large and active part in its economy, in spite of embargoes and sanctions imposed by Western countries.
The Historical Pattern: Embargoed States Always Find a Way
Embargoes and sanctions are some of the oldest techniques in a states arsenal. In this context. an embargo or sanction is an offical ban on trade or commerical activity placed on a country, thus limiting that countries ability to generate income from commercial exports. Embargos have been used to:
- Interfere with a countires ability to form positive relations with other countries (as trade and business are common ways to achieve this)
- Limit a countires military strength by forcing a them to focus on internal infrastructure development instead of war fighting
- Allow one economically and politically superior power to control another, more inferior power through the use of soft power dynamics (Not having to formally invade and conquer the embargoed country)
- Cause a country to behave in a political, social, or economical way thats advantageous or aligns with the values of the country issuing the embargo
In short, it can be ineffective, expensive, or counter-productive to a states objectives to completely dominate another state through military force, particularly if that state doesn’t have the infrastructure or excess funding themselves to maintain control of the state they are dominating. Sun Tzu made a number of points in the Art of War that speak to this:
“Give the enemy a way out”
“Do not press a desperate enemy”
“Let the enemy retreat”
— paraphrased exerpts from Chapter 7: Scroll of Military Combat. (Art of War, Sun Tzu)
If you’d like to read the Art of War for yourself and want an accessible version, my friend Antony Cummins’ version “The Ultimate Art of War” is the one I recommend.
While Sun Tzu was mainly referring to dealing with armies here, the principles still apply. For example:
- If you completely dominate an enemy, and don’t have the infrastructure to govern the state after a war, you create opportunities for rebellion, costing you more money and lives to contain
- If you throw everything at a desperate enemy, you breed resentment and allow political outliers to take power
- If you give the enemy an “out”, even though you have the power to destroy them, they may fall in line faster, shortening a conflict
Yes, what I’ve said above isn’t universally applicable, some counterpoints including:
- The treaty of Versailles after the First World War completely crippled Germany’s economy, which created the conditions for the Nazi party to take power, which they did by selling a solution to the German working class who suffered the most
- The United States of America and Great Britain agreed upon dropping two Atomic Bombs on Hiroshima and Nagasaki, an overwhelming show of force to the world which forced Japan to surrender
That said, an argument with Japan is that before World War II, America placed incredibly heavy embargoes on Japan, who at the time was heavily reliant on American oil to fuel its economy and campaign of Asian expansion. In desperation, Japan attacks Pearl Harbour on December 7th, 1941 with the aim of knocking the American pacific fleet out and forcing America to capitulate, and allowing Japan the breathing room to invade China and obtain the resources they were so desperate for. The thing is, although the Atomic Bombs resulted in quick surrender, the threshold was so extreme, costly, and politically toxic that no modern state could reasonably deploy such a tool; it worked so well because it was used once, and never since.
Economic pressure does not eliminate the will of a determined state. It redirects it; creating the conditions for a shadow economy.
Enter North Korea: The Modern Shadow Economy
North Korea has stolen an estimated $6.75 billion from the global financial system through cyber operations — $2 billion of that in 2025 alone, all without overt military action.
The Democratic People’s Republic of Korea (DPRK) has been subject to international sanctions for decades. The United Nations, the United States, the European Union, and a coalition of Western allies have systematically targeted every conventional revenue stream available to the regime, including arms exports, coal, iron, seafood, textiles, and financial transactions. The intent is familiar by now. Economic strangulation as a substitute for military confrontation. Force the regime to the negotiating table, or watch it collapse under its own weight. That said, modern technology has enabled them to avoid collapsing, arguably, the DPRK is thriving.
Before North Korea was using cybercrime to generate revenue in a meaningful way, it primarily relied on an institution whose job it is to operate as an off the books revenue engine, Office 39. Office 39 (aka Central Committee Bureau 39 of the Workers Party of Korea) is the North Korean state apparatus responsible for maintaining a foreign currency “slush fund” for the DPRK’s weapons of mass destruction (WMD) program, generating foreign currency through covert business operations overseas. Because of all of the sanctions and embargoes placed upon North Korea (guidance here), Office 39 has been associated with the production and distribution of controlled substances (drugs), smuggling, and the procurement and transfer of luxury goods both domestically and internationally.
Two such examples below show how the effect the DPRK has had on the rest of thr world when acting through its shadow economy:
The Superdollars Operation: North Korea produced counterfeit $100 bills of such quality that the US Treasury was forced to redesign the note entirely. These bills circulated for decades through diplomatic pouches and front companies across multiple countries. In 2005, the US Treasury designated Banco Delta Asia, a Macau-based bank, as a primary money laundering concern under the USA PATRIOT Act, citing its role in processing North Korean funds derived from counterfeit currency, drug trafficking, and smuggling. Around $25 million in DPRK-linked accounts were frozen. The sanctions hadn’t stopped North Korea from generating revenue; they had simply pushed that revenue generation overseas, laundering it through the United States.
State-Level Drug Trafficking: North Korea’s association with the production and distribution of controlled substances is well documented. Methamphetamine manufactured at state level was distributed across Asia through networks specifically designed to be difficult to attribute back to Pyongyang. This state level production and distribution of Class A drugs is estimated to have brought in around $100-$200 million dollars annually, though this is speculation based on very scant evidence and shouldn’t be taken as gospel.
What’s worth exploring however, is how North Korea’s state-sanctioned cybercriminal operations have, in just a few years outstripped and outpaced profits made from moving physical goods.
How the DPRK Uses Cyber to Circumvent International Embargoes
So, to kick things off here, a little history lesson is in order to be able to plug cyber into context. Before Kim Jong-un assumed power in 2011, North Korea was ruled by Kim Jong-il, Kim Jong-un’s father. Kim Jong-il strengthened the countries military strength and equipment through human captial, given North Korea didn’t really have a strong IT infrasturcture back then. Kim Jong-un on the other hand had spent his early years outside North Korea, studying computer science at the International School of Berne in Switzerland. Given this academic background, Kim Jong-un, unlike his father, seemingly realised the potential of an offensive cyber army early into his dictatorship, and began developing North Korea’s offensive cyber capability.
As far as we know, the offensive cyber capability today falls under the purvue of the Reconnaissance General Bureau (RGB), the DPRK’s primary intelligence agency, in particiular, a division known as Unit 121. The testimony of Kim Heung-Kwang, a North Korean defector highlights that Unit 121 back in 2015 had around 1,800 cyber-trained soliders. Since then, that figure appears to be closer to 6,000.
- Unit 180: Targets financial technologies and systems
- Unit 91: Compromising and stealing technology relating to neuclear and long range missile systems
- Lab 110: Military intelligence arm using cyber capabilities
Information around the Units were primarly obtained through interviews with defectors, which should be taken with a pinch of salt, yet what is clear is that North Korea uses cyber attacks to develop its military, economic, and intelligence gathering capabilities.
What’s interesting is that Unit 121 has been known to operate out of a hotel in Shenyang, China, a building majority owned by a North Korean business entity; with internet access and operational support provided through Chinese infrastructure. In 2019, the Chinese company with primary investment in the building, Dandong Hongxiang Industrial Development, was indicted by the United States for conducting illicit financial dealings on behalf of sanctioned North Korean entities involved in WMD proliferation. Given that China sits on the UN Security Council and has power to vote on the sanctions levied against North Korea, but also having companies in it’s country aiding Unit 121 in attacks against the West, there is something to be said about the danger of a nation playing both sides.
Between 2009 and 2013, North Korea was beginning to launch attacks against finance organisations, governments, and broadcasting bodies, deploying wiper malware and causing destruction. The cyberattack that put North Korea on the map though as a serious cyber threat was the Sony Pictures attack in 2014. At this time, Sony created a comedy film depicting the assassination of Kim Jong-un, and given North Korea’s intention to be taken seriously as a nation, must have landed poorly with its leadership. Let’s refer to The Prince by Niccolo Machiavelli (online copy available here) for context as to why the North Korean state may see this as an issue:
“It makes him contemptible to be considered fickle, frivolous, effeminate, mean-spirited, irresolute, from all of which a prince should guard himself”
“That prince who creates such an opinion of himself has a great reputation; and it is difficult to conspire against a man with such a reputation and difficult to attack him, provided that he is understood to be of great ability and revered by his subjects”
— Chapter 19: The Prince, Niccolo Machiavelli
In short, with Kim Jong-un being a dictator, the state relies on the absolute strength and aura of the dictator, and if they are challenged by external factors (basically negative PR or propoganda) with no reprisal, the subjects of that country may begin to question how strong the dictators grip really is; which, if left too long breeds rebellions and conspiracies.
So in terms of how the Sony Pictures attack played out, attackers stole corporate sensitive data including employee details, salaries, private executive communications, and unreliased films (which were leaked on the internet and made free to everyone to watch). This caused a ripple effect across Sony and it’s supply chain. Employees had to be terminated, cast and production costs for the movies (million of dollars) hadn’t been paid, and the reputational damage caused brought the company to its knees.
Following the attack, the attackers then deployed wiper malware — Backdoor.Destover, which destroyed Sony’s internal infrastructure and forced the company to shut down entirely. Sony brought in Mandiant to help remidiate and recover from the attack, The damage was already done though, and the point had been made; the North Koren state was prepared to reach into a private American company and tear it apart to protect its reputation.
Historically, a representative or body residing in one state insulting the leadership of another state would at times lead to conflict. Though, with the modern political climate being what it is, raising an army and attacking the United States for the actions of a private company would be absurd, with cyber there is a sense of deniability, it’s a lot cheaper than military action, and it caused serious damage to their target; making it the perfect option that best benefitted North Korea at the time.
Moving away from the realm of attacking private enterprises for political reasons, North Korea’s cyber operations evolved significantly towards financially motivated attacks, specifically targeting the emerging world of Web3 and cryptocurrency.
Web3 refers to a decentralised iteration of the internet built on blockchain technology. At its core are smart contracts - self executing agreements written in code that run on blockchain networks without the need for a central authority or intermediary. In theory this makes transactions trustless and transparent. In practice, it also means that if someone finds a vulnerability in that code, there is not alot that can be done; the DPRK has clearly noticed huge potential here.
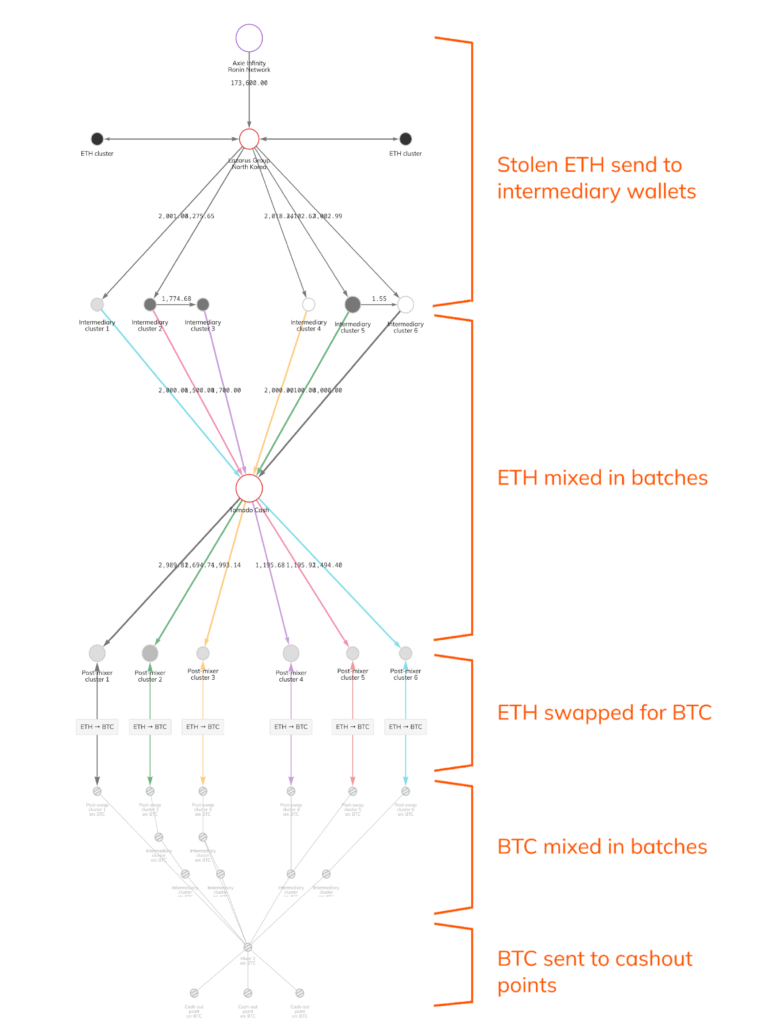
In 2022, attackers compromised the Ronin Network — a blockchain bridge built to support the popular play-to-earn game Axie Infinity. By gaining control of five of the nine private keys used to validate transactions on the bridge, they authorised two fraudulent withdrawals totalling approximately $625 million in Ethereum and USDC. The FBI and US Treasury formally attributed the attack to Lazarus Group and APT38, both North Korean state-backed entities. It remains one of the largest crypto heists in history. Chainanalysis was able to seize around $30 million dollars of the $625 million stolen.
Source: Chainanalysis
Then in February 2025, Lazarus Group surpassed that with the Bybit breach, which saw $1.5 billion extracted from the Dubai-based exchange, the largest single crypto heist ever recorded. This time the attack wasn’t a smart contract exploit. It was a supply chain compromise and UI manipulation, attackers compromised a developer machine at Safe{Wallet}, injected malicious JavaScript into the signing interface, and manipulated what Bybit’s authorised signers saw, causing them to unknowingly approve fraudulent transactions.
That destination, according to the US Treasury and UN sanctions monitoring reports, is North Korea’s weapons programmes. The stolen cryptocurrency, converted through Chinese-language money laundering networks and mixing services funds the same ballistic missile and WMD development that the international sanctions regime was specifically designed to prevent.
Why Sanctions Alone May be Insufficient
Sanctions and embargoes against North Korea are not without merit. They have constrained access to materials needed for conventional military development, limited North Korea’s ability to engage in legitimate international trade, and imposed real economic costs on the regime. Nobody serious is arguing they should be lifted. But the historical record, and the evidence of the last decade specifically, raises an uncomfortable question about whether sanctions alone are sufficient.
Let’s look at the pattern. Every significant tightening of the sanctions regime against North Korea has been followed by an escalation in cyber activity, and none can deny the evolution and maturity of North Korea’s cyber strategy. The more the conventional revenue streams get closed off, the more aggressive and sophisticated the cyber programme becomes. Bureau 39 didn’t scale up drug trafficking because sanctions were working, it likely did so because sanctions were closing other doors. The cyber programme didn’t emerge from nowhere, it emerged from a state that had spent decades adapting to economic pressure and, as of today, are pretty effective at it.
Cassius Dio, writing in the third century AD, observed in Roman History Book 44 that “successes have always been greater and more frequent in the case both of cities and of individuals under kings than under popular rule.” He wasn’t wrong. A dictatorship (an unequivical leader) can commit to a twenty year offensive cyber strategy without an election, a budget cycle, or a change of government interrupting it. A dictator in power isn’t subject to democratic red tape, allowing the entire country can pull in one direction, the benefits of a single leader. Maybe there is an analysis to be done on whether it is better to be feared or loved, and what that can do to a country…
The White House acknowledged in 2023 that up to half of North Korea’s missile programme is funded through cyber theft. That figure alone should prompt a serious conversation about whether the current approach is working as intended. The sanctions were designed to starve the weapons programme of resources. Instead the weapons programme found a new funding source that the sanctions architecture was never designed to close.
Going back to the beginning of the blog, we know that Napoleon tightened the Continental System repeatedly. Each tightening produced more sophisticated smuggling networks out of Britain, not less. The blockade runners got faster, the documentation fraudsters got better, and the corrupt officials got more numerous. The pattern with North Korea’s cyber programme is the same. Each round of sanctions has been met with a more capable, more aggressive, and more creative response.
The question worth asking isn’t whether to sanction. It’s whether sanctions without a serious complementary strategy to address the digital economy North Korea has built around them can ever be sufficient on their own.
Closing
North Korea has stolen billions, wormed its way into Western countries to steal intelligence through operations like DreamJob and Contagious Interview, are building a nuclear programme, and kept their economy running, all while under some of the most comprehensive sanctions ever imposed. The DPRK isn’t slowing down. If anything, the operations are getting larger, more targeted, and harder to trace with every passing year.